Welcome back to the Patchstack Weekly security update! This update is for week 13 of 2022.
This week, I will talk about two high-risk vulnerabilities in two WordPress plugins with one big difference: One was patched, one was not.
In this week’s knowledge share I will share some new WP-CLI Security commands that were just added. I hope you’ve heard of WP-CLI, if not, then you are in for a nice surprise!
Vulnerability news
Product Table for WooCommerce – Unauthenticated Arbitrary Function Call

The Product Table for the WooCommerce plugin had an unauthenticated function call vulnerability patched this week.
I strongly suggest updating this plugin on your sites as soon as possible. This vulnerability is a high risk, as an arbitrary function means any PHP function could be running on affected websites.
Ad Injection plugin – Stored Cross-Site Scripting (XSS) & RCE
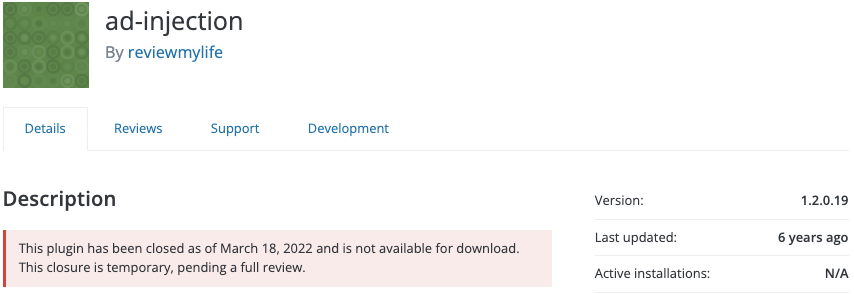
The ad injection plugin is affected by two vulnerabilities, one a stored cross-site scripting, the other being more serious: Remote Code Execution.
The good news is, it appears these security bugs require high privileged accounts to exploit.
The bad news is, the plugin has not received a patch in 6 years and has been downloaded on average a dozen times a day. So, a lot of site owners are currently out of luck with no option to patch this potentially abandoned plugin at this time.
Safe SVG – SVG Sanitization Bypass

Last week I mentioned the safe SVG plugin/library, and I missed that there was a recent security patch in this library which could have led to a bypass of SVG file sanitization steps.
Looking at the changelog entry for this update also highlights the value of open-source software when it is done right. There were a dozen developers who contributed in some way to help the safe-SVG plugin with the 1.9.10 release.
These developers are likely using safe-SVG, in their projects, and are helping give back, fixing issues not just for themselves, but for everyone using the shared project.
Weekly knowledge
New WP-CLI Security Commands
In this week’s knowledge share, I would like to talk about the command-line tool, WP-CLI and a new set of WP-CLI security commands that were just added.
What is WP-CLI?
WP-CLI is a powerhouse tool for performing manual and automated tasks on your WordPress website. The only pre-requisite is, you need SSH access and the package installed, most major hosting providers such as Pagely or Cloudways have it pre-installed for you.
WP-CLI can do almost any administrative task on your website, but I want to talk with you today about some recently added security tools WP-CLI has available.
New security-specific commands to WP-CLI
Just last week, during the Cloudfest Hackathon in Europa-Park Germany. One of the team’s projects was adding a handful of new security-specific commands to WP-CLI.
These new features were added by a great team of developers from multiple companies like Mint hosting, Cloudways, T-Systems online, Codeable, IONOS, and more.
You can find more details about WP-CLI secure commands, including credits, features, and more at HacktheWP.com
But I will list a few of the new WP-CLI secure features for you now:
- Add one or more, or all, security HTTP headers to your website, such as HSTS Referrer-Policy, X-Content-Type-Options, X-Frame-Options, and X-XSS-Protection.
- Block access to sensitive files or directories, such as the wp-config.php, wp-admin/install.php, .git, cache, and many more. You can even set your own custom file or directory block rules.
- Block bots from enumerating usernames by iterating over author IDs.
- Block direct access or execution of PHP code in certain directories. It is really handy to block execution of PHP files that ended up in the uploads directory, if you ask me.
- Turn off file listing on directories without an index file.
- Verify integrity of WordPress core files, just like WP-CLI core verify-checksums
- Disable the file editor in WordPress.
- Set “sane” permissions for all files and directories in the WordPress installation.
One thing that these new security commands do not do is validate if a site is running a known insecure component. Lucky for us, there already is a WP-CLI feature for that.
Patchstack has its own WP-CLI command: wp-cli patchstack which you can use in conjunction with the Patchstack ThreatFeed API.
The Patchsatck WP-CLI add-on gets its data of which components are vulnerable from Patchstack’s meticulously managed database of WordPress vulnerabilities, or just the Patchstack database.
Vulnerabilities added to the Patchstack database are sourced from multiple public sources such as MITRE, as well as from the great team of security researchers who contribute bugs to the Patchstack Alliance (we also report the valid Patchstack Alliance security bugs to MITRE, to make sure this information is public.)
With both of these security-oriented features added to your WP-CLI installation, you can easily automate many of your WordPress administration security tasks.
Thanks and appreciation
This week’s thanks go out to the team behind WP-CLI-secure-commands, you did great at the CLOUDFEST Hackathon 2022. I look forward to seeing more.
A thank you is due for the Product Table for WooCommerce plugin developers. Thank you for releasing the patch that addressed this serious issue. Now it is up to the site owners to push the update to their websites.
Thanks go out again this week to the developers who contribute to the safe-svg plugin. There are too many to name, so check out the safe-svg changelogs yourself.
And a special thank you to everyone who supports Patchstack and our efforts. Customers, Alliance team members, and everyone who shared our white paper in a positive or negative light, and discussed it in the last few weeks. Together, we’re improving the world of open-source security.
I will be back next week with more security tips, tricks, opinions, and news on the Patchstack Weekly security update!


