The fastest vulnerability mitigation for WordPress
Did you know that, in 2024, 33% of all vulnerabilities in the WordPress ecosystem received no fix from the developer? Patchstack will protect you.
Patchstack neutralizes vulnerabilities before they can be exploited
Patchstack combines deep application visibility (SCA), threat intelligence (TI) and context-aware prioritization (KEV)
About RapidMitigateNew proactive approach
- A vulnerability is detected on the website
- A rule is auto-triggered only on-demand
- The vulnerability is secured against attacks
- User resolves the vulnerability by updating to the patched version when convenient
Old reactive approach
- The website becomes vulnerable
- The website is attacked and compromized
- The website needs to be manually remediated
- Website can be re-compromized until resolved
"The most exciting company in the WordPress security space."
Joost de Valk
Founder of YoastSEO
Developer
Best for professionals and agencies who build and maintain websites that need uncompromized security.
Get first month freeEnterprise
Best for businesses who require advanced security, maintain high profile websites, compliance, and security at scale.
Request quoteWebhost
Extend your hosting platform with integrated vulnerability mitigation.
Patchstack for hostsLooking for Enterprise-level volumes, SLA, DPA?
Pricing and featuresSecurity finally meets simplicity
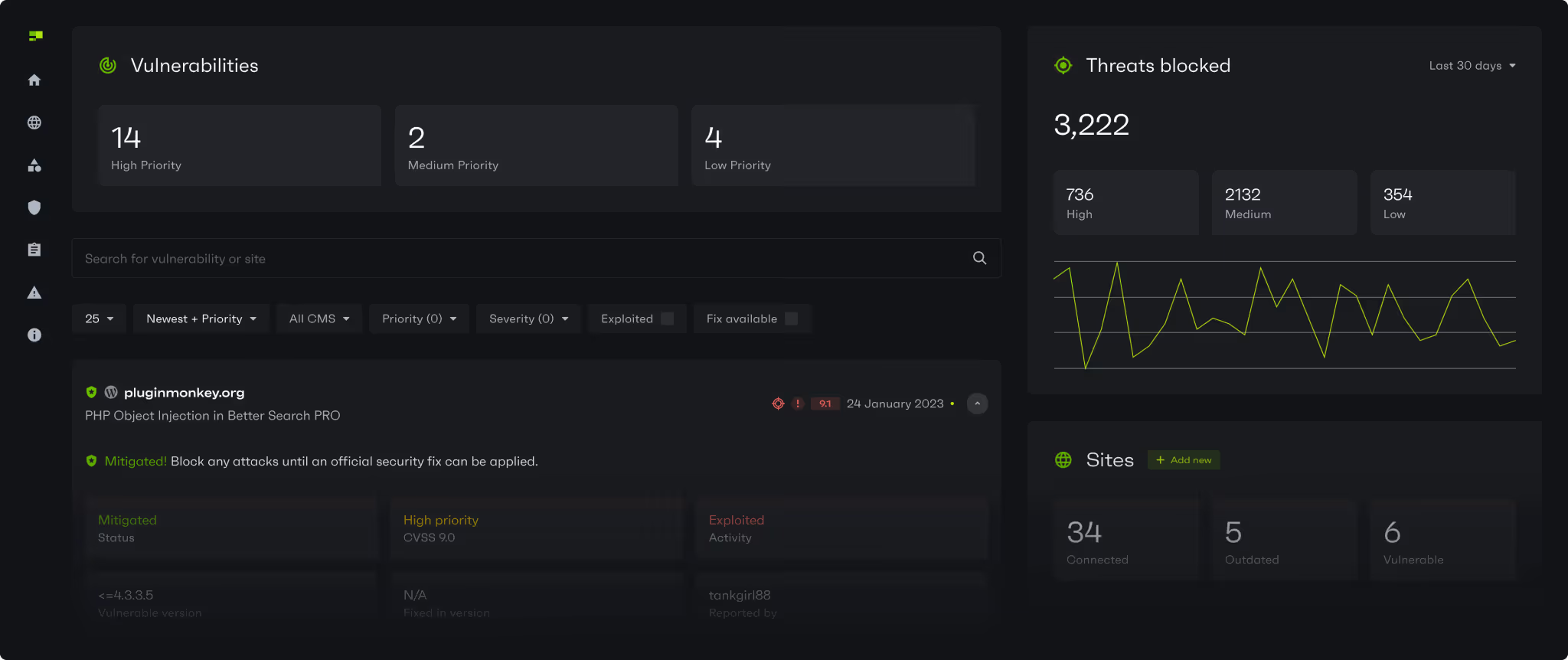
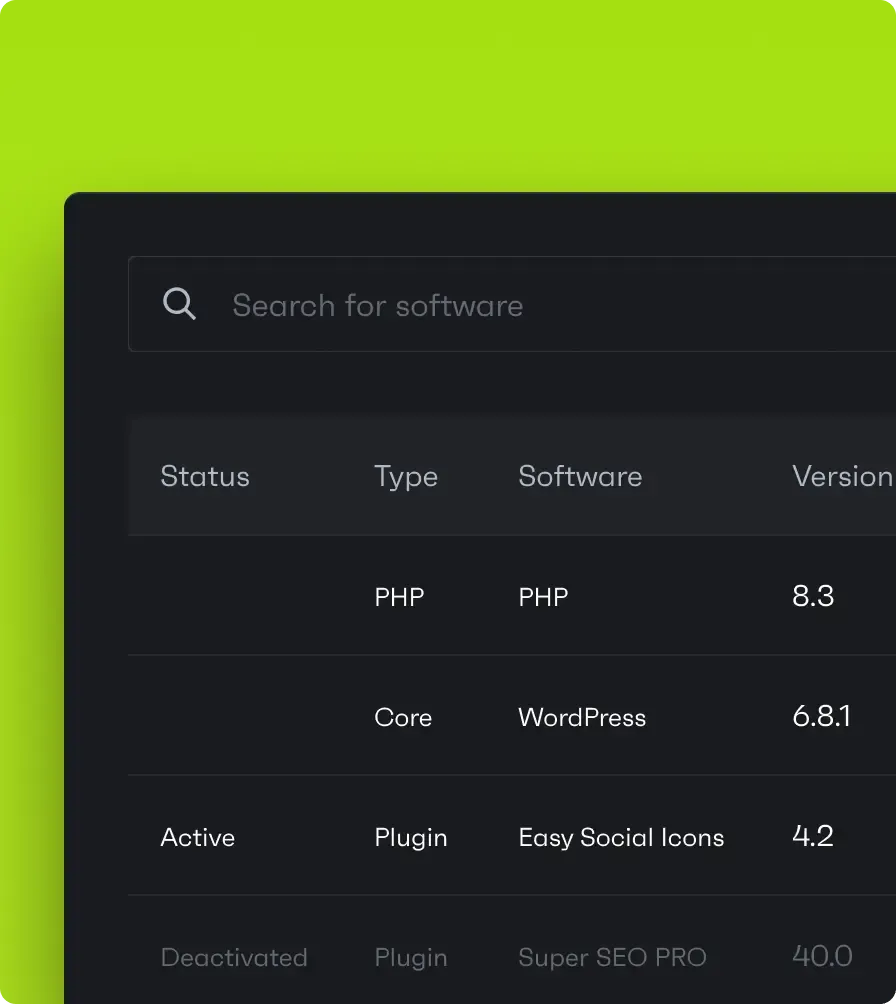
Vulnerabilities in open-source are publicly known and easily targeted in large-surface attacks. Patchstack mitigates threats in 3 easy steps:
Get first month freeAnalysis (SCA)
Prioritization (KEV)
Mitigation
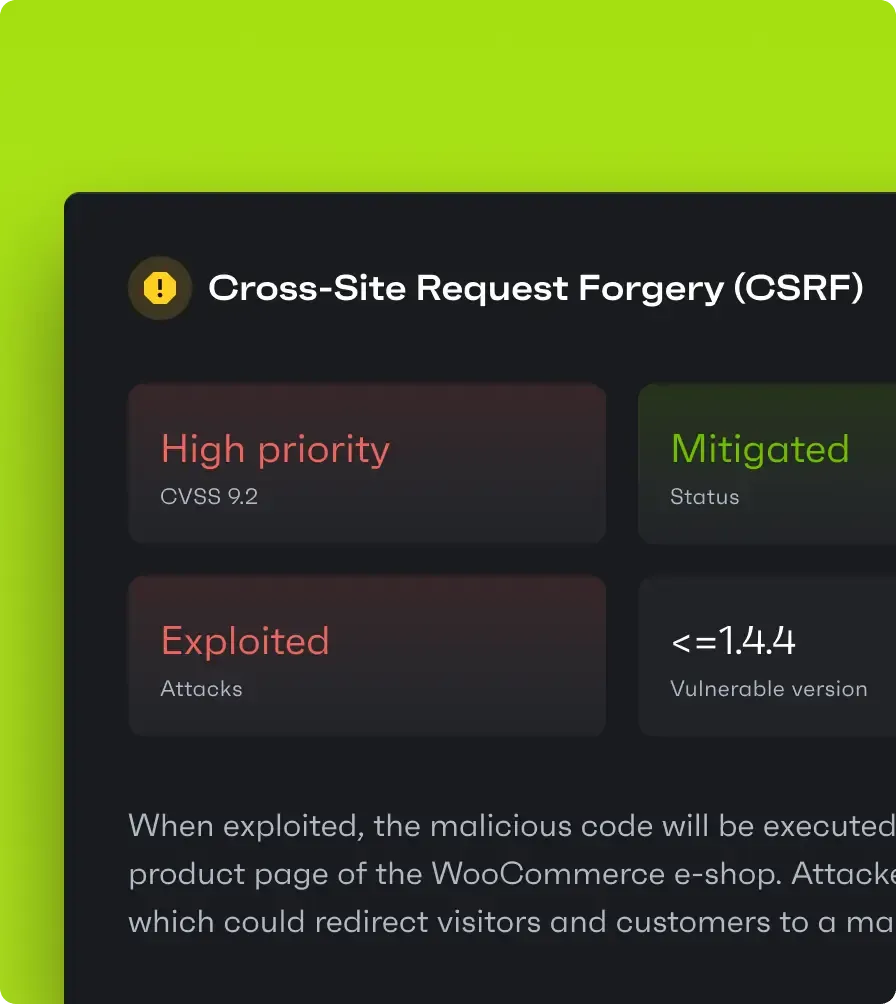

With vulnerabilities being weaponized in minutes, being first really does matter
Patchstack processes the most security vulnerabilities globally and protects you up to 48h before public disclosure
#1
Global processor (CNA) of vulnerability intelligence51%
Of all 2024 WordPress security disclosuresProtection modules make WordPress security easy
Protect websites from takeover, defacement, malware injection, ransomware, SEO spam, traffic redirection, SEO ranking drops, Google penalties, and more.
RapidMitigate
Hardening
Additional protection rules to block common malicious requests against WordPress.IP Blocklist
Block IPs known for attacks and contribute threat data back to other users.Build your own workflow using API
Deliver monthly security reports, manage vulnerabilities within your existing dashboard, block attackers at the network level via DNS firewall, sync data with Enterprise SIEM/SOC tools, and build powerful automations.
Don't just take our word for it
Protect your WordPress websites from vulnerabilities
Developer
Best for professionals and agencies who build and maintain websites that need uncompromized security.
Get first month freeEnterprise
Best for businesses who require advanced security, maintain high profile websites, compliance, and security at scale.
Request quoteWebhost
Extend your hosting platform with integrated vulnerability mitigation.
Patchstack for hostsLooking for Enterprise-level volumes, SLA, DPA?
Pricing and featuresWhat the FAQ
Can I get Patchstack elsewhere with a discount?
Why would a hacker target my websites?
What if my website has already been hacked?
What is the difference between a WAF and RapidMitigate?
I already use other security tools. Do I need Patchstack?
Will Patchstack slow down my websites?
Will Patchstack plugin help my site pass PCI-DSS, SOC2, ISO 127001 or other security checks?
Still have questions? Reach out to Sander via live chat.