Turn security from an expense into a revenue-driver
The only WordPress security solution built for hosting providers — protect your customers, reduce support load, and unlock a new revenue stream.
100%
High markup makes security well worth the investment Contact sales15H
Weekly reduced WordPress support workload Read case studyAnnual recurring revenue projection
Total additional revenue after 5 years
$0
You could earn $0/yr — let's build your plan
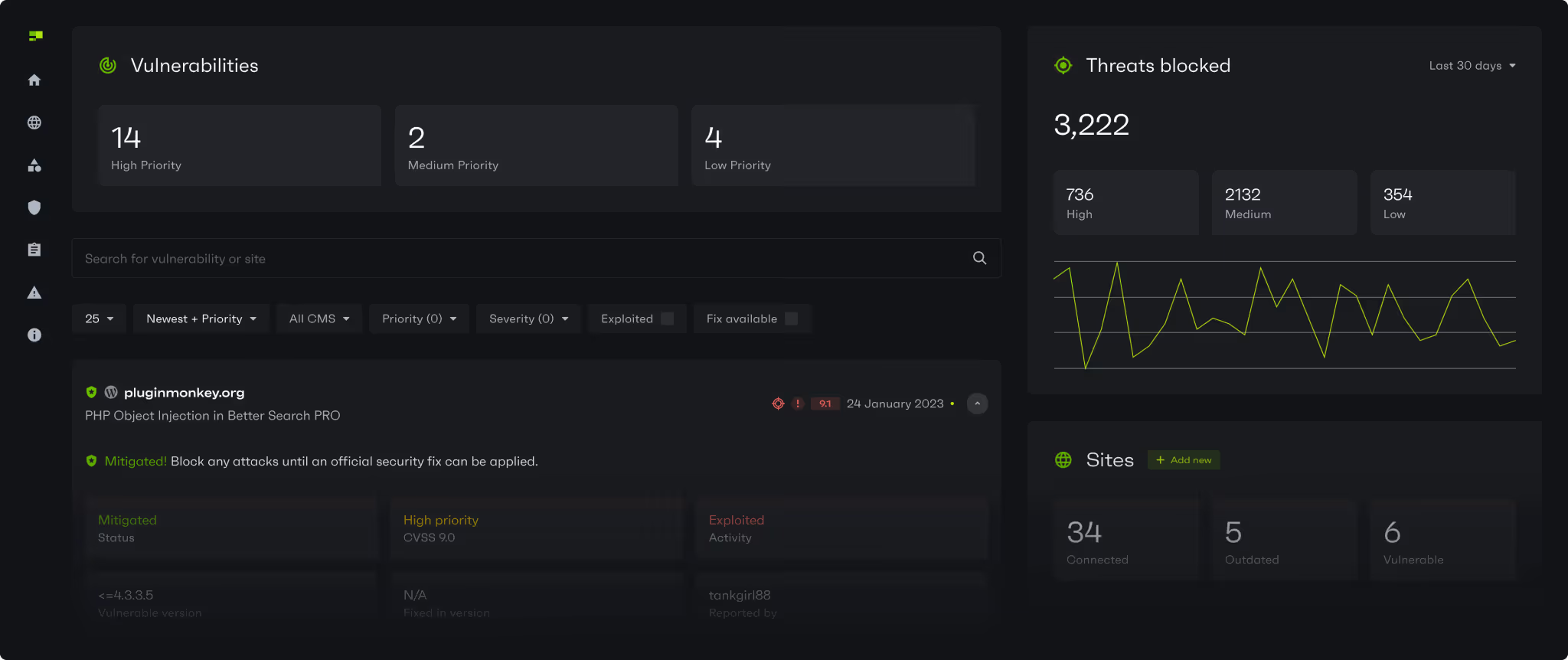
Contact salesYour current security stack is missing 74% of WordPress exploits
74% of vulnerability exploits bypass widely applied web hosting defenses including Imunify360, Monarx and Cloudflare.
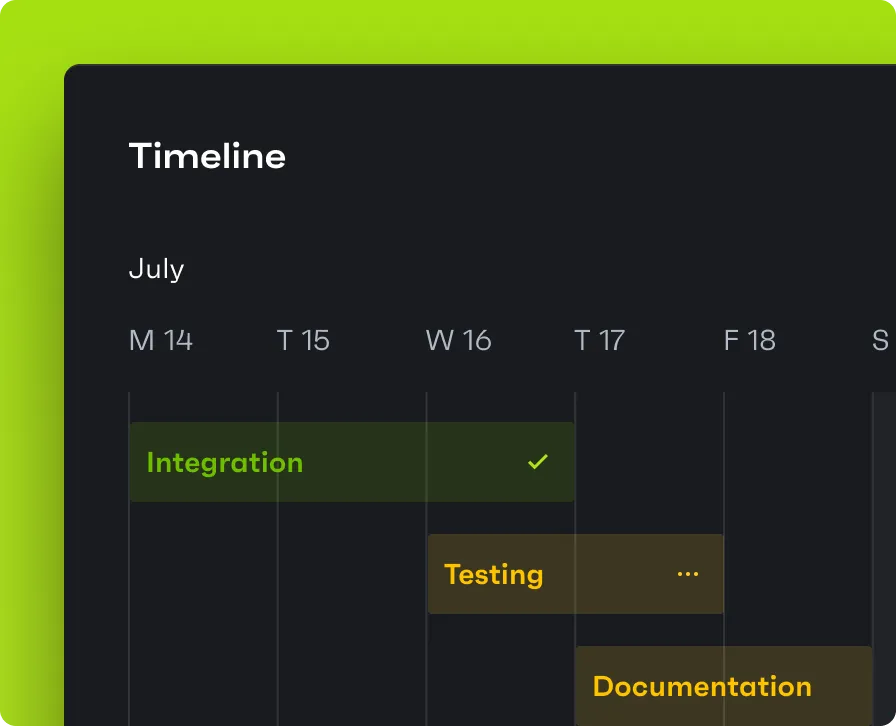
Instant protection
When a threat is detected, Patchstack automatically deploys mitigation rules across your customers sites.No code changes
Mitigation rules are highly targeted and do not change source code, cause conflicts or false positives.Lightweight
Patchstack is reported up to 10x less resource-intensive than always-deployed generic solutions targeting patterns.Designed to prevent generic attacks, WAFs fall short at stopping specific threats because they do not understand context.
| Comparison | Patchstack | Imunify360 | Cloudflare |
|---|---|---|---|
| Security layer | Application-level | Server-level WAF | Network-level WAF |
| Method | Combination of WAF, SCA, threat intelligence and dynamic rule deployment | Pattern-based rules | Signature-based filtering |
| Mitigation rules | 12,640 specific rules | Limited | Limited |
| Precision | Highly targeted and deployed only-on demand saving you resources | Generic, all rules deployed even if not needed | Generic, all rules deployed even if not needed |
| Speed to new rules | Instantly, deployed in real-time | Slower (rule updates depend on vendor cycles) | Slowest (rules need to be optimized to reduce false positives) |
| False positives | None | Medium (generic rules) | Medium (broad filtering) |
| Performance impact | None | Low to moderate | Low to moderate |
| Visibility into application | Limited | ||
| Session awareness | |||
| User auth awareness |
"In the first month, Patchstack has blocked 631.5k+ threats across sites using WP Umbrella. We also converted 4.5% of sites to our Patchstack-powered add-on, creating an additional revenue stream."
Aurelio Volle
Founder of WP Umbrella
With AI, new vulnerabilities are being mass exploited in just hours
As the #1 global handler of vulnerability intelligence, Patchstack can mitigate vulnerabilities up to 48h ahead of public disclosure and competitors who rely on our data.
12K+
Highly targeted mitigation rules ready to be deployed, the largest on the market4.1K+
Vulnerabilities disclosed in 2024, of which 13% were highly exploitable900
Plugins installed on millions of sites have set Patchstack as a security point of contact"Over the last 6 months, Patchstack has protected our users from 1.3 million vulnerabilities."
Wes Tatters
Managing director
Integrate in days, not months
No infrastructure changes
Mitigation rules are deployed directly to the website for optimal performance.Plug and play dashboard widget
Quickly show value to users and how you help protect them to drive adoption.We support our partners’ success
We equip partners with all the essential knowledge and support you need to succeed.
Partners HubRollout plan
Partner and product playbook
Technical and marketing support