The focus of this blog post is to explain how and why WordPress sites get hacked.
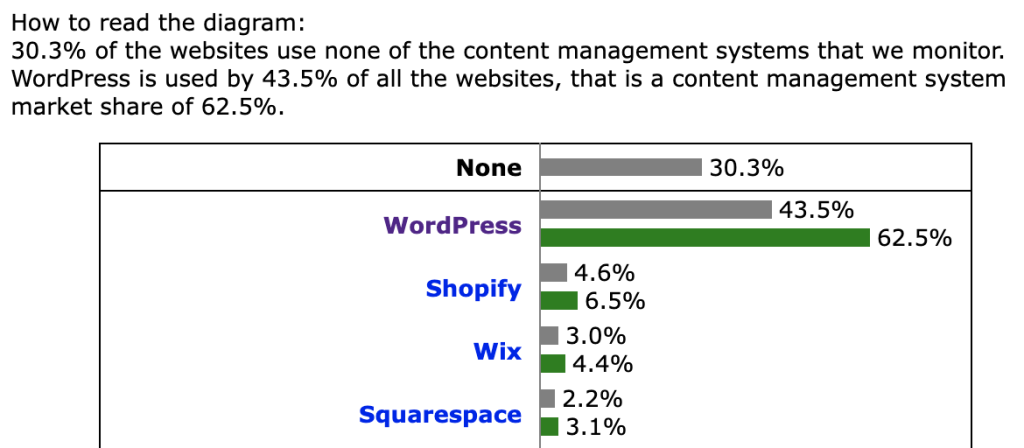
Firstly, WordPress is the most popular content management system (CMS) in the world, by far. Almost 40 percent of all websites in the world run on WordPress.
BuiltWith tracks over 27 million websites live WordPress sites. That’s a staggering number, an influence similar to Google’s hold over search engines.
However, unlike Google, WordPress is open source and has helped almost anyone create a website with relative ease. This doesn’t mean only small brands and individual blogs use the platform.
Rolling Stones, The Walt Disney Company, TechCrunch, and The New Yorker all run on WordPress, as does over 43% of the entire internet.
However, the ecosystem is so impressive in scope that it’s impossible to keep hackers away from WordPress sites. It’s just too popular and the payout is often worth the effort.
And you reading this article, may have experienced the same – seeing that your WordPress keeps getting hacked. It’s not as uncommon as you might think.
So is WordPress secure? To make it clear – there’s nothing wrong with WordPress itself, but such a popular open-source ecosystem created for a broad user base means there will be vulnerabilities.
Why WordPress sites get hacked?
If you have a WordPress website, you should definitely know why WordPress sites get hacked. Hackers aren’t necessarily targeting your website.
They’re using common vulnerabilities and executing hacks on a large scale hoping it succeeds on as many websites as possible.
However, it is also true that 43 percent of all cyberattacks are aimed at small businesses. What makes it worse is that only 14 percent are prepared for an attack, which explains why they’re targeted.
The obvious motive is financial gain. If you do have sensitive information, like payment details, then security should be a top priority.
These statistics, though, don’t mean that your website is safe from a hack because you don’t have sensitive information. Hackers have other uses for your website.
Have you ever heard of SEO spam?
SEO spam is a growing malware category. It’s reported as the most common problem. GoDaddy stated that 62% of their client sites contain SEO spam. This means SEO is a major reason to compromise a website’s security.
If you’ve worked on improving SEO, you should know how important link building is for your site. Black hat SEO tries to hijack this process. They use illegal ways to improve rankings of spam or malicious websites.
Essentially, spam content is introduced into your website. Hackers can introduce anything from whole pages of spam content to links that redirect users to pages you do not want to be associated with.
Now, imagine hundreds of hacked websites, all providing links to a website that’s chosen by the hacker. It’s worth the effort if they can get a lot more search traffic, thanks to improved rankings.
Of course, when Google finds out that you’re providing a number of links to suspicious websites, they will blacklist your website.
Malware in WordPress – another major problem
Your website can also be used to host and deliver malware. Malware on your website can probe visitors’ systems for vulnerabilities.
Hackers could be looking to take control of their systems to be part of a ‘botnet’, a connected set of systems that can be used for illegal activities.
Or just hold them to a ransom by locking them out of their system. For example, between 2014 and 2016, over 100,000 WordPress and Joomla websites were redirecting visitors to an exploit that used browser vulnerabilities to infect operating systems.
Of course, if you’re a blog creating content on contentious issues, it’s always possible that you could become a target. Hackers have the means to disrupt your services.
Finally, it might seem silly, but hackers also have to practice their skills. They’re often creating programs to test WordPress vulnerabilities.
They might not do anything to your website, but it’s never good to have your website under someone else’s control.
A vulnerable website can impact millions of users
Being the most popular CMS means that vulnerabilities will have an enormous impact. Just a few vulnerable websites can impact thousands or millions of users.
According to WordPress, its users create 70 million new posts every month. That translates into a lot of traffic.
WordPress also accounts for 43% of the most popular one million websites in the world. Some 409 million people access 20 billion WordPress pages every month.
With such numbers to target, it would be efficient to choose WordPress sites. Hackers don’t usually target a specific website. They usually write a program that identifies vulnerabilities in a WordPress site.
Once they know there’s a way to hack a website because of a common vulnerability, they target a large number of websites at the same time. It’s like casting a wide net and whatever gets caught in it is the prize.
Why are there so many vulnerabilities in WordPress sites?
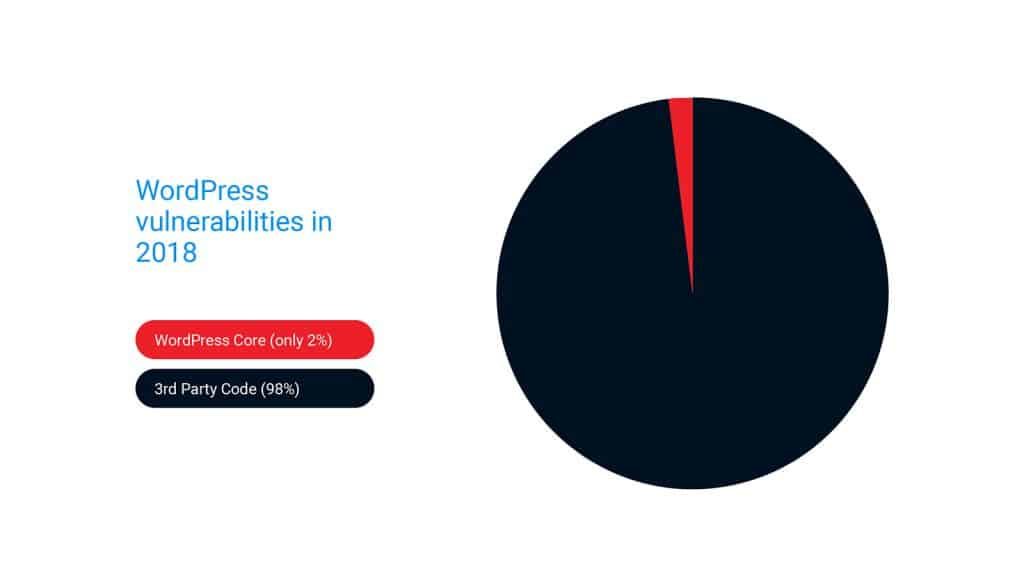
Well, it’s not WordPress core itself. It’s usually plugins and themes that make websites vulnerable.
Of course, using older versions of WordPress can leave you vulnerable as well. New versions often fix vulnerabilities while adding new features. According to WordPress, only 37.5 percent of users have updated to version 5.5, their latest.
At least 79.2 percent have updated to version 5 or newer. That still leaves millions of websites running older versions.
Way back in 2012, it was reported that Reuters was using an outdated version of WordPress when the site was hacked. That’s a big breach of a big company.
Users often refuse to update because it could break their website. Well, all you need to do is backup your site. Whenever something happens, you can always restore the backup. It’s also a good security precaution.
Now, WordPress has always encouraged developers to engage with its open-source system.
This has resulted in an incredible number of plugins (57,870) and themes (7,906), which make the CMS vastly more useful for people who want to build websites.
WordPress sites get hacked because of vulnerabilities in plugins and themes
The security of plugins is not always on an expert level, plugin developers are not security experts. They don’t have to be.
There is usually no malicious intent in security lapses, but these vulnerabilities are why most hacks happen on WordPress websites. It’s so prevalent that estimates show 98% of WordPress vulnerabilities to be related to plugins.
A vulnerability in a plugin becomes common knowledge pretty fast because it’s an open-source ecosystem. If hackers can exploit the vulnerability before a patch is released, anyone who installed the plugin is at risk. A popular plugin can have thousands or more users.
Unfortunately, often, a patch to secure the vulnerability doesn’t help. WordPress users or WordPress developers oftentimes are not developers per se but more specialists who put WordPress sites together from pieces.
The knowledge of how to manage security comes with experience, and therefore, tasks like updates may not be a priority in the beginning.
Updates are crucial
Keep in mind that updates are crucial. Outdated plugins and themes are the number one reason for websites getting hacked.
A common example from the early days is TimThumb, a plugin to resize images. A vulnerability in the plugin allowed hackers to upload malicious PHP files to websites.
The problem was made bigger because TimThumb was bundled with multiple themes. Some users weren’t even aware their websites were vulnerable as they did not know all the tools that came with their theme.
Maintaining any website requires an awareness of the WordPress ecosystem. Keep track of what’s happening, especially news on hacks and updates.
Just like updating WordPress, users sometimes decide against updating themes or plugins because it could break their current setup. It doesn’t mean you can continue to use unsupported versions.
It’s best to learn how to test updates without breaking your website. If a plugin or theme you use has stopped receiving support from the developer, find an alternative.
“Orphaned” plugins and themes have lost the developer’s interest and will probably never be updated. If you don’t get an update for six months or longer, be careful.
How to keep a WordPress website secure?
WordPress sites get hacked, that is a fact, but what should you do about it? Here are some basic things you could do without needing too much technical know-how:
Weak password use is a big problem: Passwords, like for every digital service, is the first line of defense for your WordPress website.
A weak password can give someone admin privileges. It might seem silly, but far too many people use weak passwords. Read more about how to manage passwords here.
Get a web application firewall (WAF): This is a big step in assuring increased security. A managed WAF keeps up with the latest software releases and bug fixes.
Vulnerabilities in WordPress plugins and themes are the number one reason why websites get hacked. For example, the Patchstack web application firewall is automatically updated to prevent plugin and theme vulnerabilities.
Two-factor authentication: Try to set up WordPress two-factor authentication. It adds a second layer of security.

Keep a WordPress activity log: It’s a simple but useful practice. An activity log will have all major changes on your website. Take a quick look at it every time you log in. Read more about logs here.
Backup your website online: Backups allow you to restore your site in case something happens. Once again, there are plugins to do this.
These are basic measures. If you want more security, it’s best to approach the experts. The open-source nature of WordPress also means that cybersecurity expertise is available for your WordPress website. Patchstack specializes in plugin vulnerability protection to keep your website secure.
Frequently asked questions about how WordPress sites get hacked
This question is hard to answer since there is no definitive data about that. Many sites are hacked even without site owners or managers’ knowledge. What can be said about WordPress hacking statistics is that there is an attack every 39 seconds on average on the web, but an attack does not always mean a hacked website.
On average 30,000 new websites are hacked every day and the most common way websites get hacked is by an automated tool.
With WordPress sites – hackers try to exploit vulnerabilities in popular plugins and search for websites using specific plugins that have vulnerabilities. This is when a firewall with vPatches can protect you.
WordPress websites are a top target for hackers because of their massive user base. BuiltWith tracks over 30 million websites live WordPress sites (data from March 2022).
The threat is not with WordPress itself, but the wide range of third-party plugins that are used by WordPress users. While WordPress is constantly updating its core, improved security does not extend to its plugins which are built by third-party developers.