In this article, you can read about the latest website hacking statistics from 2022.
These updated statistics on website hacking should give you an idea of just how difficult it is to ensure website security each passing year. Any software can be hacked if you do not deploy security measures and follow best practices.
Cybersecurity is now a frequent issue for companies. Websites get hacked every day and some of those hacks are fatal to the business.
“Cybercrime is the greatest threat to every company in the world.”
IBM’s chairman, president, and CEO
In order to give you a better idea of the current state of threats, we’ve compiled a list of must-know statistics on website hacking.
How often do hackers attack?
A study made in 2003 (remember, it's 2022 right now) found that there is an attack every 39 seconds on average on the web. Insecure usernames and passwords give attackers greater chances of success. Unfortunately, the web has grown so much that such studies are not accurate anymore.
Does every hacker attack always result in a hacked website?
An attack does not always mean a hacked website. For example, we at Patchstack see thousands of attacks targeted at the websites we protect every day.
These attacks are logged and monitored by our firewall system, and the web application firewall on the website makes sure the attacks aren’t successful.
It’s not any easier to answer how many websites are hacked every day or every year, especially because not all hacks or attacks are publicly disclosed.
Are security breaches increasing or decreasing?
A 2019 report found that security breaches had increased by 67% over the last five years.
(Source: Accenture)
However, when they do happen, a lot of records get stolen all at once.
This is true, but only when we’re talking about targeted attacks. A targeted attack is when a hacker has specifically chosen your website and is trying to find an entry point.
Attacks that are more broadly targeted at websites or web applications, in general, are implemented using automated tools. This means that an automated tool has been programmed to search for a specific vulnerability or software that has a vulnerability.
How many websites get hacked every day?
On average 30,000 new websites are hacked every day.
(Source: Forbes)
How are website hacks done?
The most common way websites get hacked is by automated tools. Hacking websites using automatic tools is popular because hackers can cast a wide net with little effort.
This is what happens with WordPress sites, hackers try to exploit vulnerabilities in popular plugins and search for websites using specific plugins that have vulnerabilities. This is when a firewall with vPatches can protect you.
How many days does it take to identify a security breach?
The average time to identify a breach in 2020 was 228 days. The average time to contain a breach was 80 days. Healthcare and financial industries spent the most time in the data breach lifecycle, 329 days and 233 days, respectively. (Source: IBM)
Has COVID-19 affected cybersecurity?
Online threats have increased by as much as six times their usual levels during the COVID-19 pandemic.
(Source: Info Security Magazine)
The FBI reported a 300% increase in the number of cybercrimes, from about 1,000 cases to between 3,000 and 4,000 cases each day.
(Source: The Hill)
WordPress security statistics for 2022
In 2022 we at Patchstack analyzed the year 2021 and wrote a whitepaper - The State of WordPress security 2021.
WordPress is the technology powering 43.2% of websites on the web in 2021, this is up from 39.5% at the end of 2020.
What is the main threat to WordPress sites?
The threat is not with WordPress itself, but the wide range of third-party plugins that are used by WordPress users. While WordPress is constantly updating its core, improved security does not extend to its plugins.
This is because WordPress is an open-source ecosystem that is reliant on third-party developers, and without plugins, users cannot extend the basic functionalities of the platform. A lot of developers or WordPress website owners have experienced attacks and hacks because of plugin vulnerabilities.
Do you want to set up auto-update for vulnerable WordPress plugins? Learn more on how to do that here.
Why are WordPress sites targeted by hackers?
WordPress websites are a top target for hackers because of their massive user base. BuiltWith tracks over 30 million websites live WordPress sites (data from March 2022).
Are WordPress themes secure?
WordPress theme vulnerabilities are just as critical as plugin vulnerabilities.
Out of the theme vulnerabilities reported in 2021, the most critical would lead to a full site compromise via an arbitrary file upload. Patchstack Alliance member Lenon Leite identified over 50 themes that had security issues in their file upload functionalities throughout 2021.
Are WordPress plugins secure?
A whopping 29% of the WordPress plugins with critical vulnerabilities reported in 2021, received no patch from their developers. (Source: The State Of WordPress Security 2021)
What kind of vulnerabilities are in WordPress plugins?
In 2021, Patchstack added nearly 1500 new vulnerabilities to the Patchstack database. These vulnerabilities were in WordPress plugins, themes, and WordPress core.
If you compare these numbers with 2020 when we saw nearly 600 new vulnerabilities, it’s clear that 2021 has been an exceptional year for the security of the WordPress ecosystem.
The WordPress.org repository leads the way as the primary source for WordPress plugins and themes. Vulnerabilities in these plugins and themes represented 91.79% of vulnerabilities added to the Patchstack database.
The remaining 8.21% of the reported vulnerabilities in 2021 were reported in premium or paid versions of the WordPress plugins or themes that are sold through other marketplaces like Envato, ThemeForest, Code Canyon, or made available for direct download only.
In 2020 we found 96.22% of vulnerabilities originate from plugins and themes. In 2021 we see that number rise to 99.42%. (Source)
50% of WordPress plugin vulnerabilities were XSS
Cross-site scripting (XSS) vulnerabilities once again topped the charts in 2021 accounting for almost 50% of the total vulnerabilities added to the Patchstack Database in 2021. Compared to 2020 – XSS vulnerabilities accounted for a bit more than 36%, in 2021 we see a rise in cross-site scripting vulnerabilities. (Source)
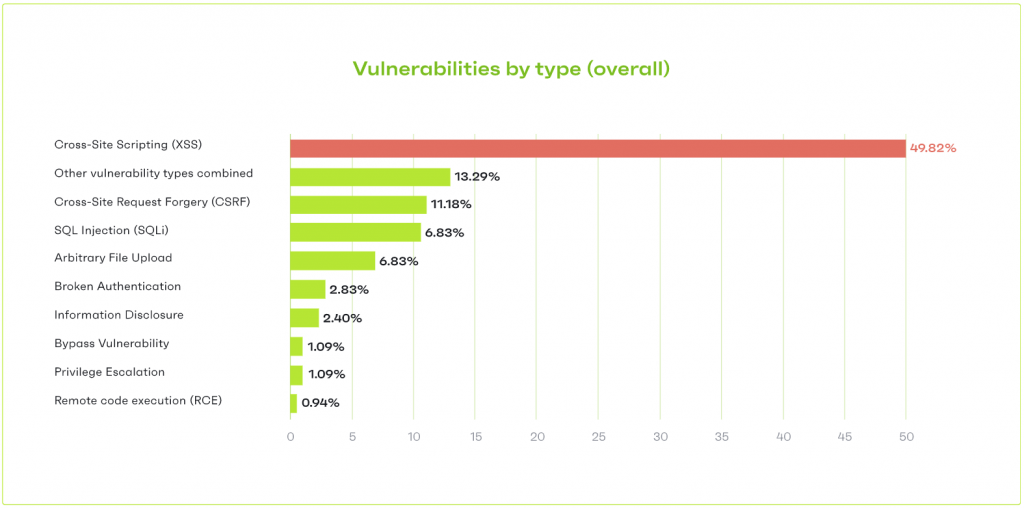
When comparing 2020 and 2021 we see CSRF and SQLi have changed places. SQL Injection counted for 9.1% of the vulnerabilities in 2020 and Cross-Site Request Forgery came third with 6.5% of vulnerabilities in 2020.
How many plugins are too many for WordPress?
The best way to keep your WordPress site secure is to keep your installed plugins count to a minimum, keep auto-updates for vulnerable plugins activated and delete a plugin if you are not actively using it.
In 2021 we analyzed about 50 000 sites and looked at the installation count of plugins and themes. We found that on average a single WordPress website has 18 different components (plugins and themes) installed.
Comparing it to 2020 where we found that an average website had 23 plugins and themes installed on a single site. It shows improvement until we compare the number of average outdated plugins and themes on a site.

In 2020 we saw 4 out of 23 components outdated and in 2021 we saw 6 out of 18 components outdated on a single WordPress site. With every additional plugin installed on the website, the risk of being exposed to a potential vulnerability increases. The fact that websites are lagging behind with updates increases the risk even more.
Have WordPress vulnerabilities increased or decreased?
We’ve seen a 150% growth in vulnerabilities reported in 2021 compared to 2020 which is a significant increase. Meanwhile, 29% of the WordPress plugins with critical vulnerabilities received no patch.
Where are WordPress vulnerabilities found?
A worrisome website hacking statistic is that over 99% of WordPress vulnerabilities are related to plugins or themes. (Source)
Website hacking statistics: web application vulnerabilities
Web applications have become the #1 target for the exploitation of vulnerabilities and, unfortunately, all kinds of software are prone to security breaches.
How many types of weaknesses are in web applications?
In 2018 researchers found around 70 types of weaknesses in web applications. As always, cross-site scripting (XSS) vulnerabilities are present in many web applications. (Source: PT Security)
Are all web applications vulnerable?
A 2019 study found that hackers could attack users in 9 out of 10 web applications they analyzed. In addition, breach of sensitive data was a threat in 68% of web applications. (Source: PT Security) It's also important to remember that there is no 100% security.
How many web applications have critical vulnerabilities?
Another 2019 study found that 46% of web applications have critical vulnerabilities, and a whopping 87% had “medium” security vulnerabilities.
(Source: Acunetix)
Four out of five web applications contained configuration errors such as default settings, standard passwords, error reporting, full path disclosure, and other information leaks that might have value for potential intruders. (Source: PT Security)
How many web applications are vulnerable to XSS?
30% of web applications are vulnerable to XSS according to Acunetix’s report “Web Application Vulnerability 2019”
What is the attackers' goal when attacking web applications?
Usually, the attacker’s goal is to get the victim to run a maliciously injected script, which is executed by a trusted web application. In this way, the cybercriminal can steal the user’s data, or even modify applications to send sensitive data to a recipient.
There are different sources for statistics on website security, and some information varies based on the scope of each study.
According to the latest ENISA Threat Landscape Report, two-thirds of web application attacks included SQL injection attacks.
Are web application attacks increasing?
There was a 52% increase in the number of web application attacks in 2019 compared with 2018.
And 84% of observed vulnerabilities in web applications were security misconfiguration. (Source: ENISA)
Web professionals worry about website security
In the second quarter of 2020, we surveyed over 300 web developers, freelancers, and digital agencies. The aim was to understand if they are worried about website security, which makes them worry, and what are challenges they want to overcome.
Are people worried about website security?
The responses to the Patchstack study done with digital agencies and developers were shocking. Two hundred forty-three (243) respondents stated that they were increasingly worried about website security.
This means over 70% of digital agencies and freelancers are worried about website security. This number was slightly higher (75%) among WordPress users.
The data also revealed that while agencies and web professionals are both increasingly worried and have challenges with regard to website security, only a little less than half (45%) take proper measures to protect the sites they’re responsible for.
During the first half of the year, we at Patchstack also noticed an increased number of attacks targeted at websites.
Since COVID-19 demanded that we move to remote work arrangements, we also used the internet much more. This resulted in increased cyber-attacks and attacks targeted at websites, which meant more work for us.
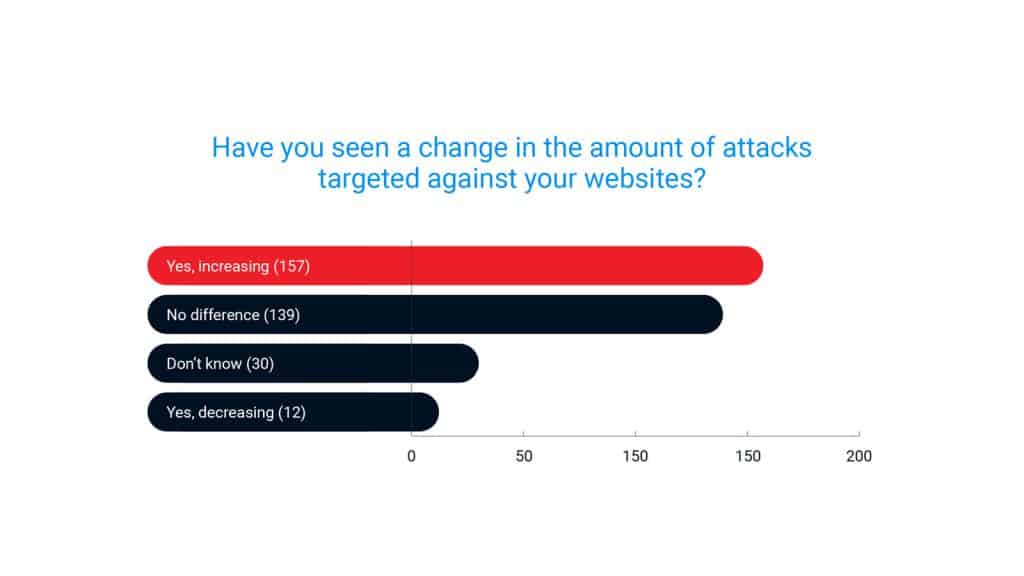
The survey backs this up as well. Almost 45% of the respondents have seen an increase in attacks targeted at websites they’re managing. We also discovered that 25% of the responders had to deal with a hacked website in the month prior to participating in the survey.
Want to read more about our findings? Download the free PDF report here.
People are more worried about a cyber-attack than a real-life attack
According to a 2018 study, Americans are more worried about cybercrime than violent crimes — including terrorism, being murdered, and being sexually assaulted.
Not only are Americans more worried about cybercrime than other crimes, but their worries about cybercrimes have been consistent for a decade now. (Source: news.gallup.com)
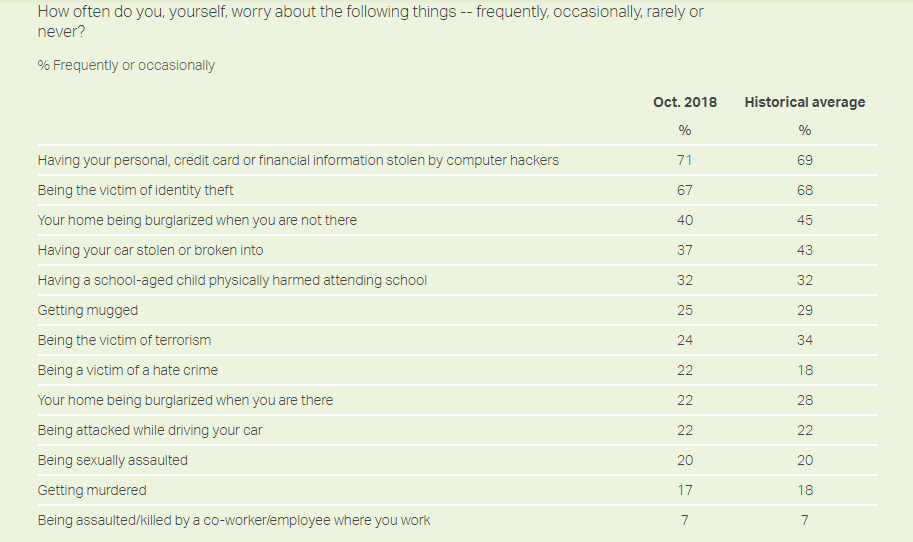
As you can see, the study states that of the 13 crimes measured, Americans continue to worry most about cybercrimes. 71% worry about the hacking of personal data while 67% about identity theft.
To put it in perspective, only 24% were worried about being a victim of terrorism, 22% about being attacked while driving, 20% about being sexually assaulted, and 17% about being murdered.
Of course, organizations are just as likely to be attacked as individuals.
A study of more than 4,000 organizations across the US, UK, Germany, Spain, and the Netherlands found that 61% reported a cybersecurity incident in 2019. In addition, 47% of small enterprises reported an incident; it was 33% in 2018.

Ironically, most organizations were unprepared and would be seriously impacted by a cyber attack. The study found that a whopping 73% of companies were not ready for a cyber attack. (Source: Hiscox)
The 2020 update of the study had a bit of a surprise. The good news — the total number of respondents who reported a cyber incident fell from 61% to 39%.
But the bad news — the median cost of an attack went up from $10,000 to $57,000. (Source: Hiscox)
Conclusion about website hacking statistics
These website hacking statistics have highlighted how important it is to always be on top of what happens with your company, the people, and the software you are using.
To be secure, you should always keep the software you use updated and monitored. Make sure you are always aware of the components/plugins you’re using on your web applications and always remove the ones that you are not using.
Choose a trustworthy hosting provider. You can learn about how to choose a hosting provider here.
It is also important to choose the right security provider for your WordPress site or any web application. When it comes to WordPress security plugins, we first recommend you get a better understanding of the WordPress security ecosystem and how they work.
Find one that can offer vPatching. Before enabling a firewall on your web app, take a look at the code.
If you haven’t got the technical skills to evaluate the chosen firewall code, let a professional help you out. Always remember that when it comes to security, do your research before buying a fancy bucket of hope. Be critical and be smart.
Frequently asked questions about website security statistics
WordPress websites are a top target for hackers because of their massive user base. BuiltWith tracks over 30 million websites live WordPress sites. The threat is not with WordPress itself, but the wide range of third-party plugins that are used by WordPress users. While WordPress is constantly updating its core, improved security does not extend to its plugins.
The most common signs you might see when your website is hacked are:
- You see a warning on the search that your site is hacked or contains malware.
- Your hosting provider contacts you or takes down your site.
- Your customers contact you.
- Google alerts you.
- Your traffic plummets and Google blacklists your site.
- You see links directing to 'fishy' sites from your website.
- Your site is suddenly very slow.
On average 30,000 new websites are hacked every day.
(Source: Forbes)
A study made in 2003 (remember, it's 2022 right now and numbers have probably risen) found that there is an attack every 39 seconds on average on the web.
WordPress websites are a top target for hackers because of their massive user base.





