Welcome back to the Patchstack Weekly security update! This update is for week 16 of 2022 and is about the power of transparency in open source, and how anyone can utilize this transparency to learn secure code review.
This week I will talk about the power of transparency in open source as it pertains to security, and how anyone, including you, can utilize this transparency to learn secure code review.
There are a lot of vulnerabilities to discuss this week as well. With some versions of Elementor being affected by an authenticated high-risk vulnerability, a development/design firm that patched many of their projects, and 9 unauthenticated SQL injection security bugs (5 with patches, and 4 without) so let’s talk vulns.
Vulnerability news
Elementor website builder – arbitrary file upload
The big vulnerability news week is related to multiple security bugs being patched in the popular Elementor website builder plugin.
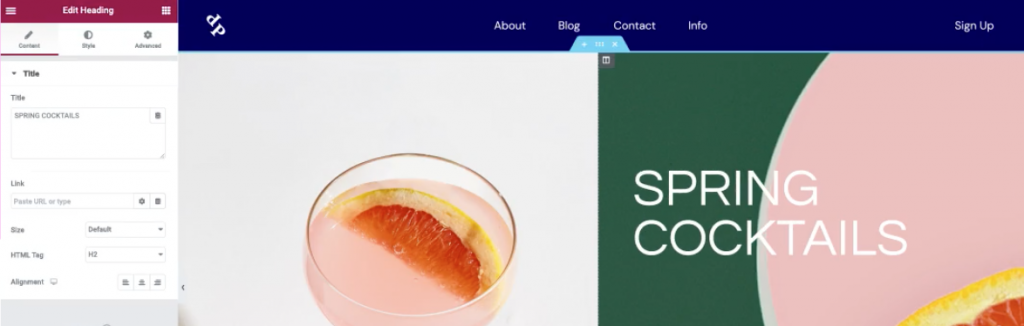
Patchstack’s own CTO Dave wrote a great breakdown of the issue in Elementor after he wrote the vPatch for all Patchstack customers.
Some key details I would like to share here are:
- The original security researcher who identified and reported this issue was Ram Gall of WordFence.
- The security bug was introduced in Elementor 3.6.0, and only affected this branch. If you’re running Elementor 3.5 or lower, that code did not have this security bug.
- The vulnerability does require authentication, subscriber-level or higher to be precise. Sites with open registration should be concerned, but any site that restricts user accounts to only trusted people is not at as high of a risk of compromise.
WBCOM Designs patch multiple plugins
The development team over at WBCOM Designs has been busy in the last week patching multiple products against reported security bugs.
Luckily, these bugs all require authentication in order for sites to be vulnerable, but it would be a good idea if you use any WBCOM Designs plugins or components on your website, please double-check if there are any updates available for those component(s) and apply them.
Multiple un-authenticated SQLi security bugs patched
If you are using any of the following plugins, please patch to the most recent version to address an unauthenticated SQLi security bug found in the code:
- Sitemap by click5
- Order Listener for WooCommerce
- Photo Gallery by 10Web
- SiteSuperCharger
- Multiple Shipping Address Woocommerce
All you need to do is apply the patch, but now for some bad news.
Users of the following plugins, you are going to need to disable or replace these plugins ASAP as there is an unauthenticated SQLi security bug just like the list above, but there is no patch available at this time:
Simple Ajax Chat – unauthenticated sensitive information disclosure
Finally, I wanted to share a vulnerability with a lower threat, an unauthenticated sensitive data disclosure security bug. It was identified by Patchstack’s very own Vlad Visse, and was patched in the Simple Ajax Chat plugin written by Jeff Star.

I was reviewing the patch and see Jeff was using a WordPress function that is new to me named wp_nonce_field This function makes it even easier than I explained back in Episode 3 when you wish to utilize nonces to secure your WordPress forms. Thank you Jeff for this great example, I learned something by reading your security patch.
I believe everyone can learn something from reading code diffs and security patches, so that will be the topic of this week’s weekly knowledge share.
Weekly knowledge about secure code review
Open-source transparency and secure code review
Transparency is one of the most powerful aspects of the open-source ideology. As it pertains to security, many people state the transparency of code helps “many eyes” spot security bugs.
But, who do these “many eyes” belong to? It would be short-sighted to say these eyes are only a group of security researchers. Those who pass through code repositories, like Ronin or Samurai for hire, identifying weaknesses and reporting issues for fun, notoriety, and possibly profit.
Instead, you could understand these many eyes as belonging to the community, the community of people who want the project to succeed, the people who want open source to succeed.
The only requirement to helping open source projects with code security is knowing how to spot security bugs.

People of any background, nationality, expertise, or experience can learn about secure code review by simply practicing the skill. They can utilize the transparency of open source to practice this skill at any time and here are a few easy ways to learn how. 👇
If you would like to understand how to identify and patch a specific vulnerability type, you can look up the patch a developer released to address such a security bug. I did this with Simple Ajax Chat this week and learned something in the process.
If you would like to learn how to code defensively, check out some of the Patchstack Weekly archives. I talk about security bugs all the time.
If you would like to learn more about what types of security bugs and vulnerabilities could affect a web application’s codebase. Check out OWASP and the OWASP Top Ten. These are the industry standard starting point for web application security.
Finally, if you would like to practice identifying or hunting for security bugs, you can utilize open-source tools like OWASP ZAP, and consider participating in the Patchstack Alliance when you find a security bug in an open-source project. Together we can help secure the world!
Thanks and appreciation
This week’s thanks go out to Jeff Star of the Simple Ajax Chat plugin, the WBCOM Design development team, Ram Gall for identifying, and the Elementor developers for patching the serious vulnerability in this extremely popular plugin.
And many more thanks go out to the numerous developers who have patched security bugs, learned secure coding practices, and to the OWASP community. And to everyone who is contributing to making the software, the open-source web relies on, to be safe and secure.
If you ever think it is a thankless job to make things more secure, just remember we see what you’re doing, and your efforts are worth it.
I will be back next week with more security tips, tricks, opinions, and news on the Patchstack Weekly security update!


