Welcome to the Patchstack Weekly Security Update, Episode 51! This update is for week 50 of 2022.
This week’s knowledge share is about a recent influx of patched security bugs affecting a single vendor. Don’t panic though, the bugs are low risk. The noteworthy part is the number of products affected by the same bug. Stay tuned for this weekly knowledge share where I explain why one vendor has multiple products affected by the same bug, and what this has to do with the software supply chain.
In this vulnerability roundup, I will cover the plugins patched from the above single bug report. Remember, they’ve all been patched (which is not always the case).
I will also provide an update for this week’s unpatched security bugs. The concerning trend continues, but the numbers are leveling out.
Securing the software supply chain
Securing the software supply chain has been in the news a lot this year. Ever since the log4j incident last year, it has been a hot subject. But, what does it really mean? What specific problem does this solve? Today I will answer those questions.
Users of software may think of it as an application they run, nothing more. We need to pull back and look at this from another perspective though – the developer’s perspective. Developers write code, but they also integrate other people’s code (via libraries, frameworks, or other means) into their projects.
The applications users use are conglomerations or collections of code. An easy way to understand this is with WordPress. A WordPress site is normally not WordPress alone, you add plugins and themes and customize it for your needs. You are, in effect, orchestrating a medley of software to build the application. Just as developers do.
Now that we know how single applications are built, and they are not stand-alone products.
This makes security, complicated
We all know it is our responsibility to update insecure software. But, what if there is a security bug in a library or component our applications use, who is responsible then? How would end users even know about the problem?
In an ideal world, the developers or architects who chose the components their projects were built on hold the responsibility to apply the updates. In turn, if needed, they also need to inform their end users about the update and it’s importance.
Enter YITH
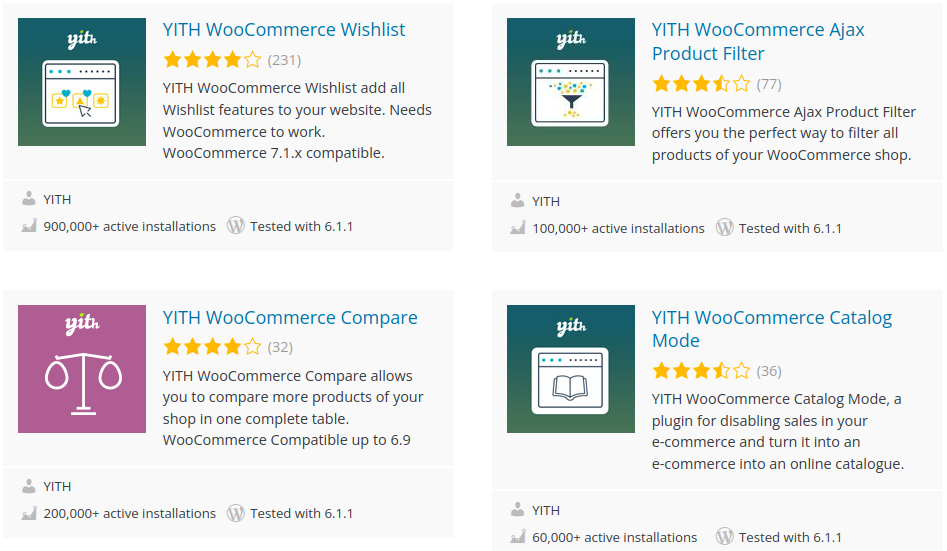
This ideal behavior is what we saw with the popular Woocommerce add-on vendor YITH. The YITH developers built in-house libraries for all of their products. Unfortunately, one of those libraries had a lower-risk security bug in them. After a little discussion with the Patchstack Alliance, the YITH developers updated their in-house library to address the bug in multiple of their projects.
This is why the Patchstack Database recently added a large number of YITH plugins. One bug in a library was patched and now all of the downstream projects that used the library are more secure and safe to use.
This was ideal. But, we all know things don’t always work out that way.
Enter SBOM
This is why there is a push from many in the security field for SBOM – or software build of materials. It is proposed that every project should include a SBOM to allow users to cross reference the project’s libraries and dependencies for security concerns.
The Patchstack App is a SBOM + alerting system already. Site owners who set up the Patchstack App on their site(s) will receive a list of installed components, plus receive automated alerts if or when any of those components have known security bugs in them.
Developers have options too, like GitHub’s dependabot which will alert developers if their repository uses an insecure dependency.
Future
In the upcoming months and years, we will likely see an increase in proactive security measures like SBOMs and alerting systems like Patchstack or dependabot. Preemptive security alerts are the future, anyone relying on security vendors who provide post-compromise detection, like an anti-virus, will be seen as two steps behind the attackers and part of the past.
Vulnerability roundup
YITH addresses 20+ security bugs
If your sites use YITH plugins, you may want to check for a security update on your sites. The Patchstack Alliance recently received reports of CSRF security bugs which affected multiple YITH plugins.
CSRF is a low risk security bug, requiring an attacker to target logged in users and get them to visit links or web pages. But, it is still worthwhile to apply these updates.
The YITH developers did a great job addressing this bug that was found in multiple projects of theirs. As I mentioned in this week’s knowledge share, the bug was in their in-house library. You could say this was one small bug patched resulting in many plugins and many websites being secured.
Unpatched security bugs.
This week’s unpatched security bug numbers are still steady. With 7 plugins in the last 7 days being closed on the WordPress repository due to lack of security bug patches. I see evidence that some of these plugin’s developers are actively working on a patch, so I wish them good luck and godspeed in their efforts to secure their customer’s websites.
Thanks and appreciation
This week’s thanks goes out to the developers at YITHemes. It was great discussing security bugs with your team, even if we had to iron out some wrinkles in the process. In the end, the YITHemes developers came through with a patch and addressed the issue acrossed all of your projects. Great job.
Every project that patches security bugs and communicates security effectively deserves recognition. There are simply too many to name, developers are patching security bugs every day.
So, further thanks is extended to the developers who are actively working on patching security bugs. Your efforts are not ignored, and I acknowledge your commitment to security and safety for your users.
I will be back next week with more security tips, tricks, opinions and news on the Patchstack Weekly Security Update!


