Welcome back to the Patchstack Weekly Security Update! This update is for week 31 of 2022.
In this week’s knowledge share, I will talk about nulled plugins and themes – how they are a hidden security risk, how they harm trust in open source, and what you can do to make things right.
I will then cover this week’s vulnerability news, which highlights 2 security bugs in abandoned plugins and 1 authenticated remote code execution bug that was recently patched.
What is a Nulled theme or plugin?
The term “nulling” comes from warez groups of the past, where they would modify software to bypass license key checks and allow users to use the software without paying. The name is a reference to the process, “nulled” software was commonly modified directly in the byte-code, the most common modification was to insert a bunch of “null” (0x00) bytes to bypass or remove the part of code that checked the license key.
Nulling open-source PHP code is trivial in comparison to reverse engineering and modifying the byte-code of compiled closed-source software. The goal remains the same though, modify the code (with PHP typically you remove lines of code, instead of adding null bytes) to bypass license key checks and allow users to use software without paying.
There ain’t no such thing as free lunch
Originally a punchline to a joke, this ancient meme still holds true almost a century later. Nulled plugins and themes sound like free lunches at first, but users pay one way or another.
It does not take much to support the open source projects you use or rely on for your business. So you should. Supporting these projects monetarily, either via donations, premium licenses, or support contracts helps the people directly responsible for the projects. With small projects, your support goes directly to helping the people involved in the project and not lining some investment bankers’ coffers.
Why do users use nulled components?
Some users of nulled components don’t know they’re using a nulled component. Surprisingly enough, some people dupe others, trick them into paying for a nulled plugin one way or another. Other times it’s intentional to reduce business expenses and pocket the extra cash.
Unfortunately being naive, or being too caught up in saving cash will turn around and cost someone in the end. First the developers of the project, in the form of lost revenue, then the users, in the form of abandonment.
What is the true cost of nulled components?
I mentioned it before, there ain’t no such thing as free lunch. The costs of using a nulled plugin are not so much financial, but risk related.
There is a risk if there is no support. Support goes both ways too. Developers and project leaders support their users if they have problems. Support also means users supporting developers for their projects. This comes in the form of more software updates, new features, and also security patches.
This results in a statement caused by nulled software not receiving updates. The process of nulling the software sometimes leaves it in a state where no updates will be made available. Leaving sites that run nulled components, that don’t support the projects, unable to update, and possibly, eventually hackable in the event of a security update being missed.
If you go to update a plugin or theme on your site and notice it stops functioning. Then you may have installed or been given a nulled version of a plugin.
If it turns out you were using a nulled plugin or theme (with or without your knowledge.) Don’t get upset, don’t be ashamed. Just make it right.
If you were using a nulled component that brought value to your website. Then it should be a no brainer to pay for it! The developers were not deceiving you, it was someone else who nulled the software and sold it to you.
There are few open source developers who can make a living off their software, and those who do charge, do not charge excessive fees. You can make things right and support the developer directly. Projects supported like this will receive regular updates and security patches.
At the least, you will know you did the right thing and are paying the people who actually built the software you are using. You can sort things out with the person who sold you the unsupported and nulled version later.
Vulnerability news
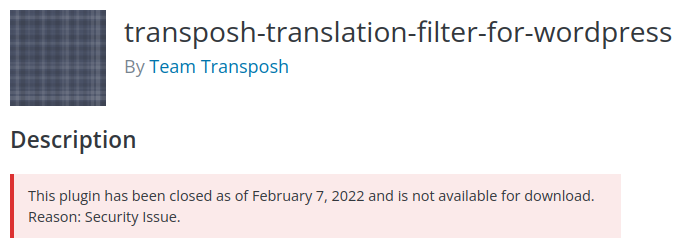
transposh-translation-filter-for-wordpress – Unauthorized Settings Change
The attack vector for this security bug was just published publicly, but this semi-popular plugin has been closed for months due to a “security issue”, likely this one. I hope that was enough time for the thousands of websites running this plugin to remove or replace it on their sites.
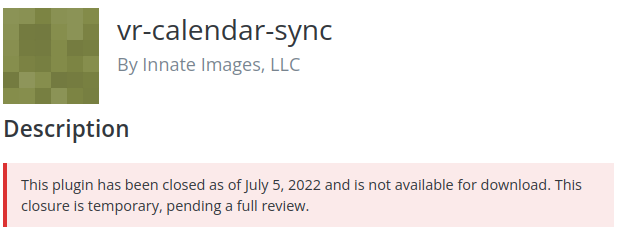
vr-calendar-sync – Unauthenticated Arbitrary Function Call
Unfortunately the vr-calendar-sync plugin appears to have been abandoned. Users of this plugin are encouraged to remove the plugin to avoid the risk posed by this security bug.
wp-dbmanager – Authenticated Remote Command Execution
Users of the WP-DBManager plugin should make sure they’ve applied all recent patches, especially if they have multiple users. The developer for this plugin addressed a security bug, which could lead to an authenticated user executing code on the web server.
Thanks and appreciation
In this week’s thanks and appreciation, I want to thank all of the users who pay for their code licenses and support the projects that they use. This addresses an important aspect of open source, the need to support the creators.
And a special thank you goes out to the developers of WP-DBManager. Thanks for looking out for your users and getting that security bug patched.
I will be back next week with more security tips, tricks, opinions and news on the Patchstack Weekly Security Update!


