Welcome one and all to the monthly Patchstack Alliance round-up!
Each month we give out rewards and recognition to our community of researchers for their contributions to finding WordPress vulnerabilities.
Below you’ll find the leaderboard and winners of June’s bug hunt.
What is Patchstack Alliance?
Patchstack Alliance is a community of ethical hackers and researchers who support the open web by finding and reporting vulnerabilities in WordPress plugins and themes.
In doing so, we help protect WordPress websites from attacks.
June 2022 summary
Our researchers had a pretty spicy month – a few of the reported vulnerable plugins had more than 100,000 active installations, and one of them even had more than 800,000 active installs.
We can say that in June, our researchers reported software that affects more than one million active websites on the Internet. Average active installation count per reported vulnerability – 79021 websites.
Let’s talk about other numbers. To measure the severity of each vulnerability, we use the CVSS (ver. 3.1) scheme and calculator. The highest CVSS score vulnerability reported by Alliance researchers in June had 9.3 (critical) base score points. It was for the plugin that has 20,000 active installs.
One of the most impressive reports we received in June had a plugin vulnerability with a 9.1 (critical) base score at a whooping 100,000 active installs!
The average CVSS base score for reports received in June was 5.2 (medium).
Besides the main prizes for the Alliance points each month, we have special bounties for vulnerabilities with the highest active install count and highest CVSS severity base score. Both special prizes were won by Rafie Muhammad, aka Yeraisci, who also took the top spot on the leaderboard this month!
Well done, Rafie – you, sir, are on a roll.
Leaderboard and winners
June’s leaderboard is as follows
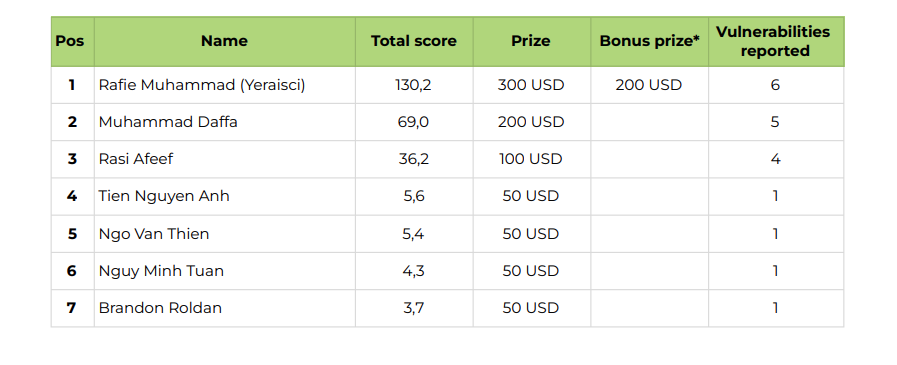
Thanks to all researchers who submitted vulnerability reports last month!
If you want to compete in the bug hunt and contribute to making WordPress safer, you can join the Patchstack Alliance here.
All valid vulnerabilities are also publicly available in our vulnerability database.