
Earn cash bounties by hunting for vulnerabilities in WordPress software
Time to squash some security bugs! Successfully report a vulnerability to sign up to our bounty platform. Read the rules.
Zeroday payouts up to $33,000
Receive generous payouts for reporting high-impact vulnerabilities
Terms and conditionsRewards
| Installs | Subs | Unauth |
|---|---|---|
| 15M+/Core | $16,500 | 🔥$33,000 |
| 5M+ | $7,200 | $14,400 |
| 1M+ | $3,600 | $7,200 |
| 500K+ | $2,450 | $4,900 |
| 100K+ | $1,300 | $2,600 |
| 50K+ | $700 | $1,400 |
| 10K+ | $300 | $600 |
| 5K+ | $200 | $400 |
| 1K+ | $125 | $250 |
Monthly TOP20 prize pool $8,850
Guaranteed in monthly payouts to TOP20 + one lucky ethical hacker
See leaderboardRewards
| 🥇 1st | $2,000 | |
| 🥈 2nd | $1,400 | |
| 🥉 3rd | $800 | |
| 4th | $600 | |
| 5th | $500 | |
| 6-10th | $400 | |
| 11-15th | $200 | |
| 16-19th | $100 | |
| 20th | $50 | |
| Random pick | $50 | |
| Random pick outside TOP20 | $50 |
Level up to unlock rewards $16,887
Earn extra rewards as you accumulate XP and level up
How to earn XPRewards
| Lvl 12 | $5,000 |
| Lvl 11 | $3,500 |
| Lvl 10 | $2,500 |
| Lvl 9 | $1,700 |
| Lvl 8 | $1,337 |
| Lvl 7 | $1,000 |
| Lvl 6 | $700 |
| Lvl 5 | $500 |
| Lvl 4 | $300 |
| Lvl 3 | $200 |
| Lvl 2 | $100 |
| Lvl 1 | $50 |
Focus on research and let Patchstack handle reporting to vendors
Join the fastest growing OS security community


Clear framework
Patchstack enforces a clear and standardized form for reporting and handling vulnerability reports faster
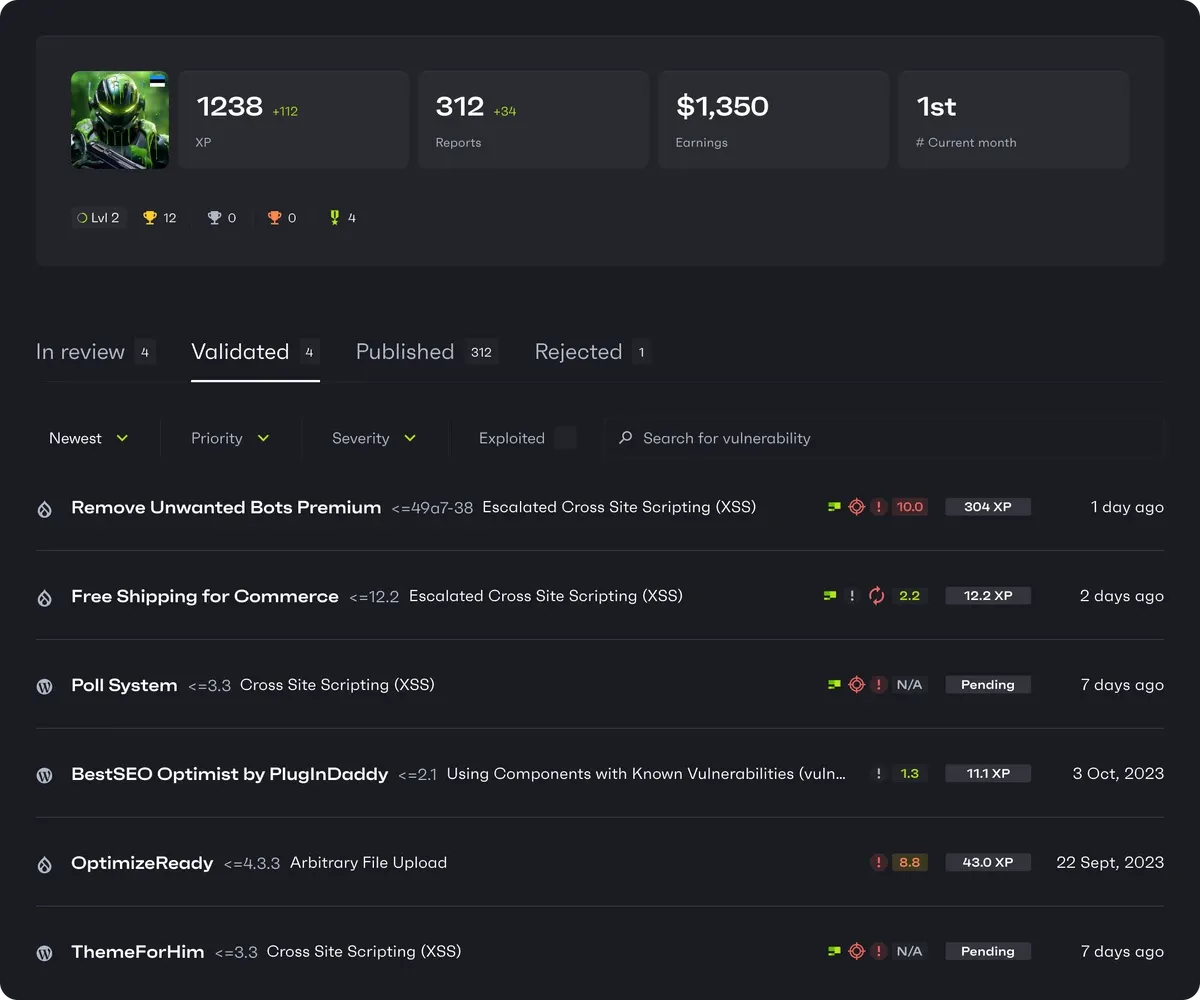
Submissions overview
Researchers can now keep track of their performance; view the status of and access all vulnerability reports in one place
Public profile
All of your reports and achievements will be displayed on your public profile. You can include socials and even a BuyMeACoffee or Paypal link
How to start your researcher profile?
1
Join the Alliance Discord and read the submissions and payout terms
2
Report a vulnerability in WordPress (plugins with a VDP earn extra XP)
3
Once verified, the CVE is published in your name and you receive an invite4
Compete for monthly bounties, 0day payouts or earn by leveling upWhat the FAQ
How are the bounties paid out?
How is XP for the monthly competition calculated?
What are the minimal requirements to receive monthly bounties?
Wait… bounties for finding vulnerabilities in FREE software?
How can I join Patchstack's Bug Bounty program?
What is Patchstack's Bug Bounty program?
If you have questions, ask the staff on our Discord.
Ready to squash some security bugs and cash those bounties?
New to bug hunting? Learn from our Academy.