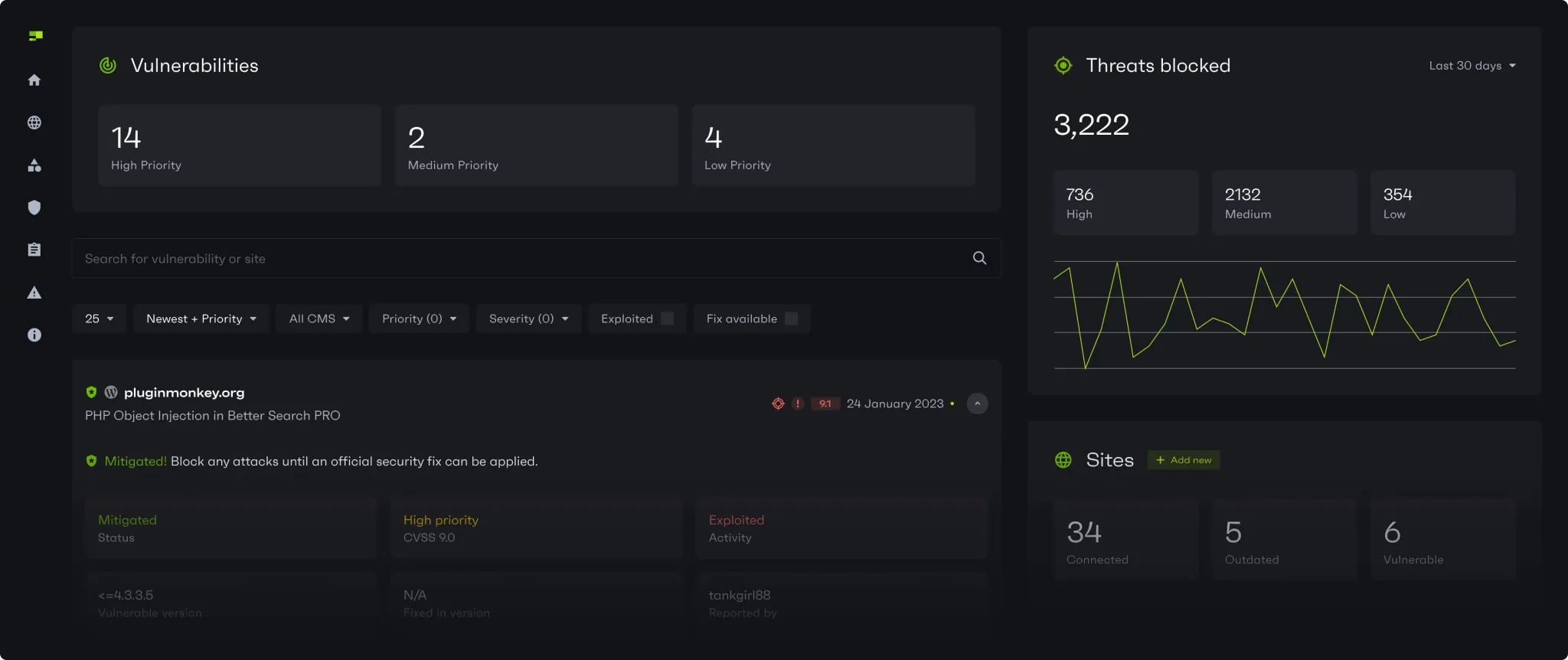
The fastest and smartest vulnerability mitigation for websites
Patchstack prevents up to 74% more vulnerabilities from being exploited compared to leading web application firewalls.
74% of vulnerability exploits still bypass leading advanced web hosting defenses
Patchstack’s RapidMitigate automatically blocks these threats with highly targeted mitigation rules, effective even for:
60%+
of attacks exploiting vulnerabilities with patches available but not applied120
during the average exposure window in days to update, test and patch a vulnerabilityWith AI, new vulnerabilities are being mass exploited in just hours
As the #1 global handler of vulnerability intelligence, Patchstack can mitigate vulnerabilities up to 48h ahead of public disclosure and competitors who rely on our data.
12K+
Highly targeted mitigation rules ready to be deployed, the largest on the market4.1K+
Vulnerabilities disclosed in 2024, of which 13% were highly exploitable900
Plugins installed on millions of sites have set Patchstack as a security point of contact"Over the last 6 months, Patchstack has protected our users from 1.3 million vulnerabilities."
Wes Tatters
Managing director
Customers want reliable security they can understand
Patchstack is a user-friendly security solution that’s simple for customers to understand and adopt.
Comply with PCI-DSS 4.0 requirements
Unmatched speed, efficiency and scalability
Patchstack is the leader in open-source vulnerability intelligence with the largest collection of mitigation rules on the market.
Find out what Patchstack can do for you.