The fastest mitigation for security vulnerabilities in open source
Patchstack is the leader in open-source vulnerability intelligence, covering the entire lifecycle from detection to mitigation.
trusted partner for
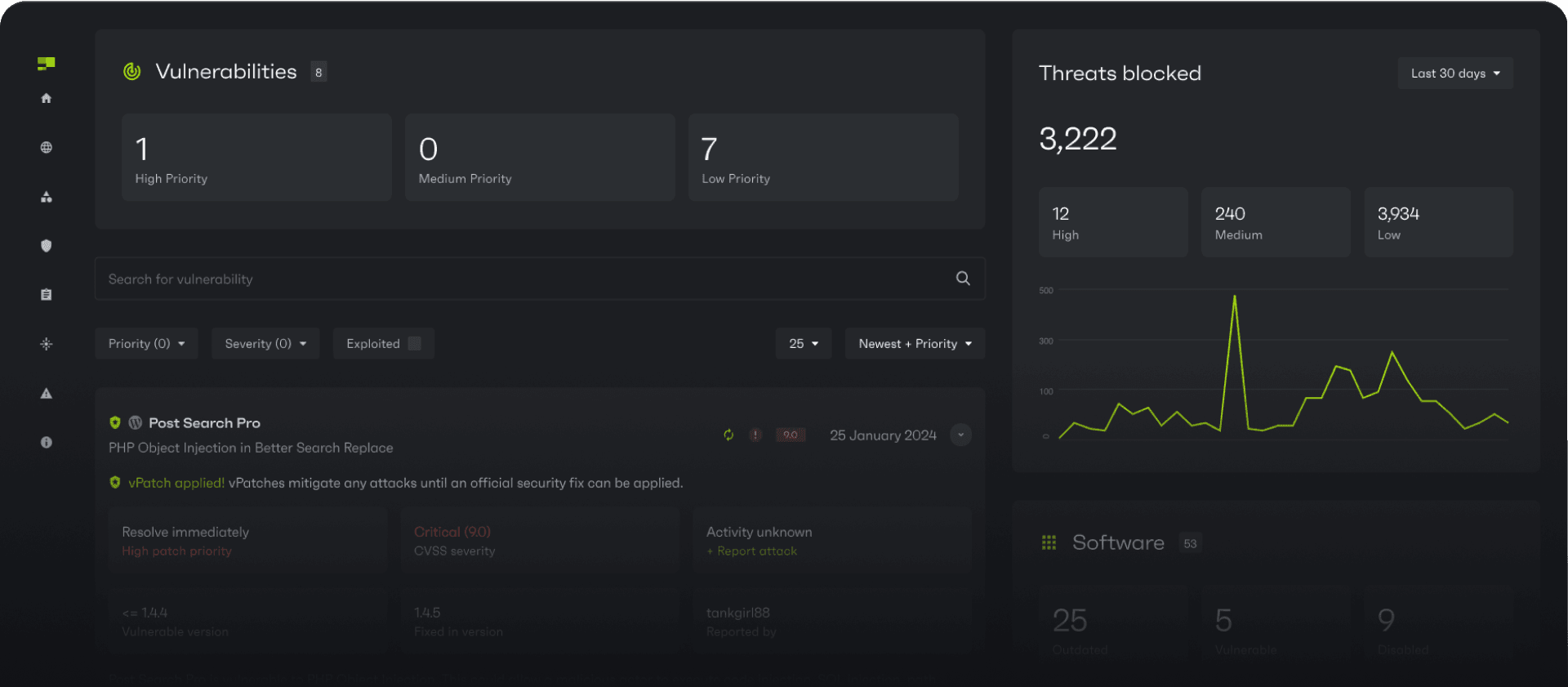
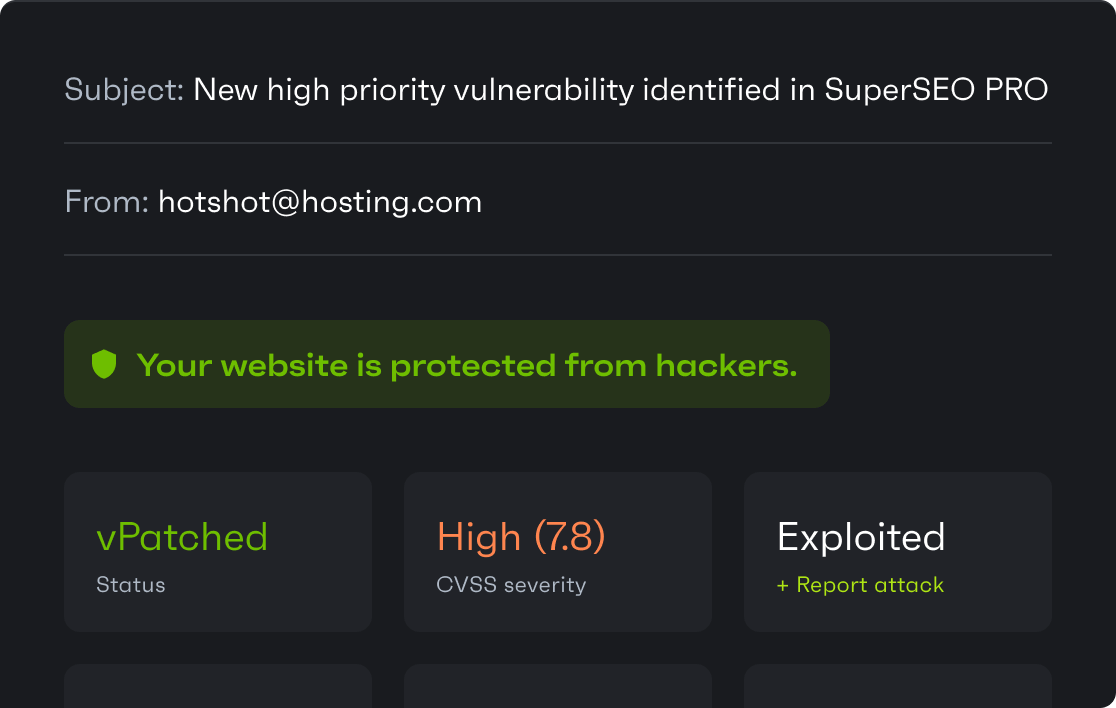
Instantly mitigate vulnerabilities in websites
With a collection of 10,000+ vulnerability-specific vPatches — the largest collection on the market — Patchstack bypasses SDLC and delivers conflict-free protection with no code changes or false positives.
“Patchstack is like CrowdStrike, but for websites!”
Lightweight and ready for scale - no-brainer for hosting companies
Generate revenue by seamlessly integrating Patchstack into your hosting panel. Patchstack proactively mitigates vulnerabilities before they can be exploited, reducing incidents and support load.
“Over the last 6 months, Patchstack has protected our users from 1.3 million vulnerabilities.”
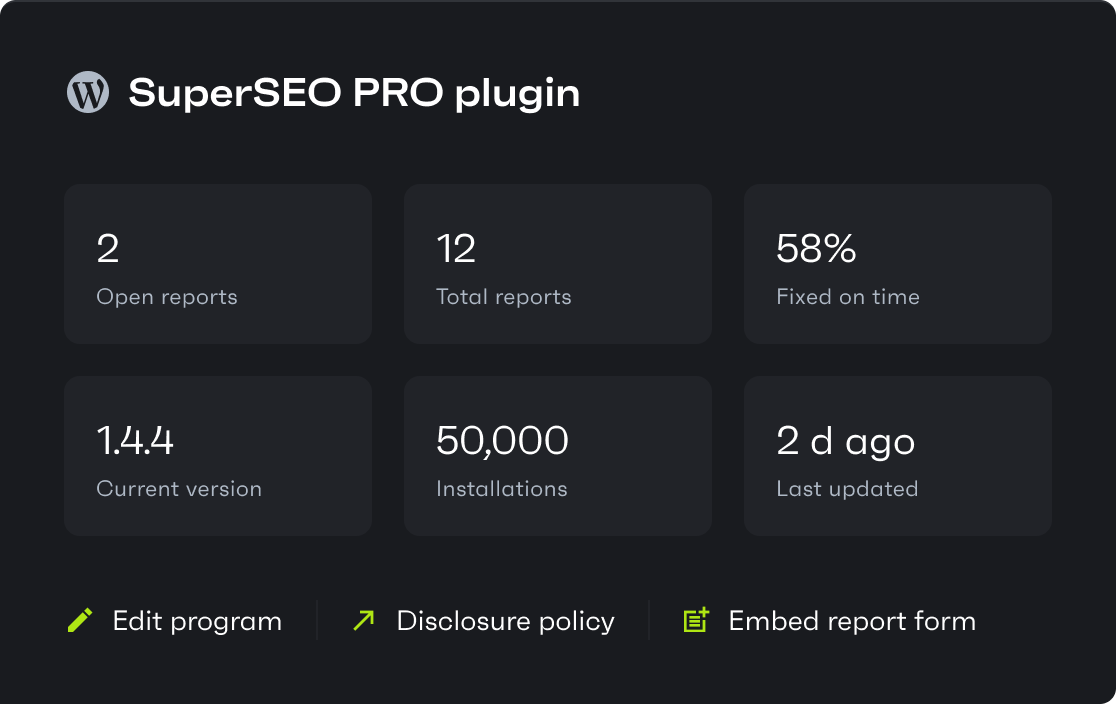
Take full control over security and gain trust by complying with CRA
Get a clear disclosure policy, receive standardized reports and expert validation. Patchstack already helps 500+ WordPress plugins comply with the Cyber Resilience Act taking effect in Q4 2024.
“For us, Patchstack is a true partner in our security efforts...”
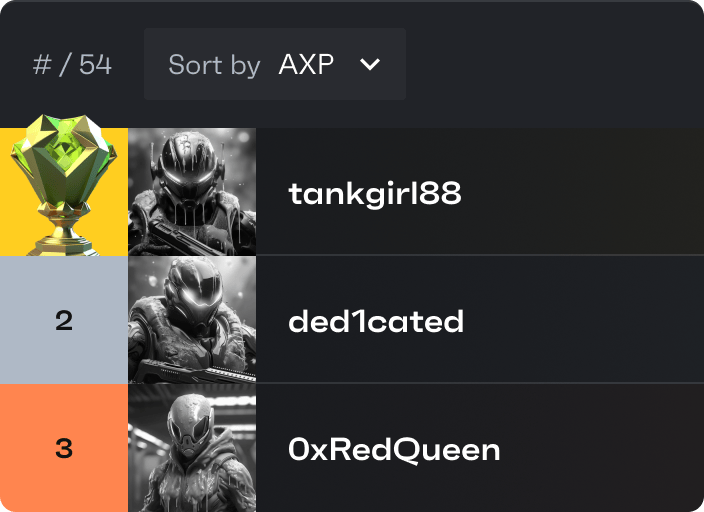
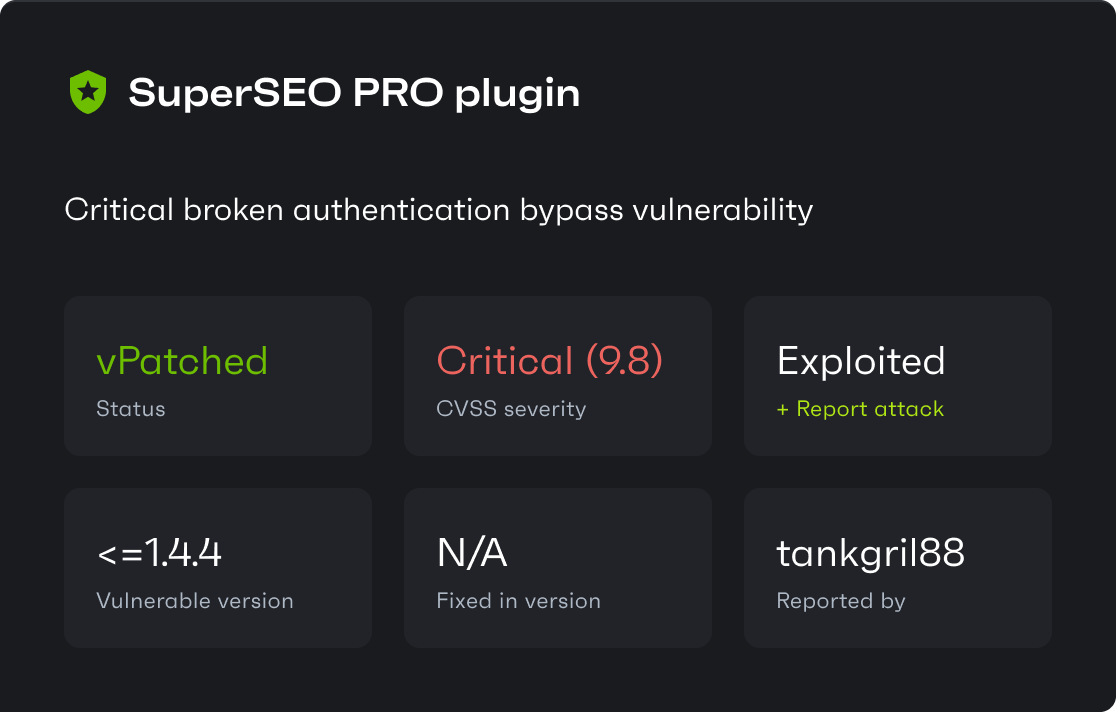
Security researcher? Help us secure open-source and earn bounties up to $14.4K
Join Patchstack’s gamified bug hunting community — track your impact, showcase your findings, and earn monthly cash payouts.