Welcome to the Patchstack Weekly Security Update, Episode 63! This update is for week 12 of 2023 and talks about how to spot abandoned plugins in your WordPress site.
This week’s news is about how to spot a silent threat that may be hiding in your WordPress plugins administration page! Stay tuned and learn how to detect the dangers of un-update-able plugins.
I will then do the vulnerability roundup, which will highlight plugins with high-risk security bugs that have no patch available.
Spotting abandoned plugins
We all know updating plugins is how you keep them secure. This is why automatic updates are so important. But, what if there are no updates available? Then that’s going to put you in a precarious position that you’re not going to be aware of.
Understanding how WordPress displays automatic updates are available will help you decipher and spot a dangerous un-updateable plugin.
How to auto-update vulnerable plugins?
To perform WordPress auto-update only on vulnerable plugins or the software installed on your websites you need to navigate to the Patchstack app Auto-Update Settings page. This allows you to see the current auto-update settings of your WordPress sites with the ability to update them on all sites individually or globally.
Learn more about auto-updates here.
First, you will need to log in to the WordPress admin panel and open the Plugins dashboard.
I’ve provided a few images of a test dashboard for these examples.
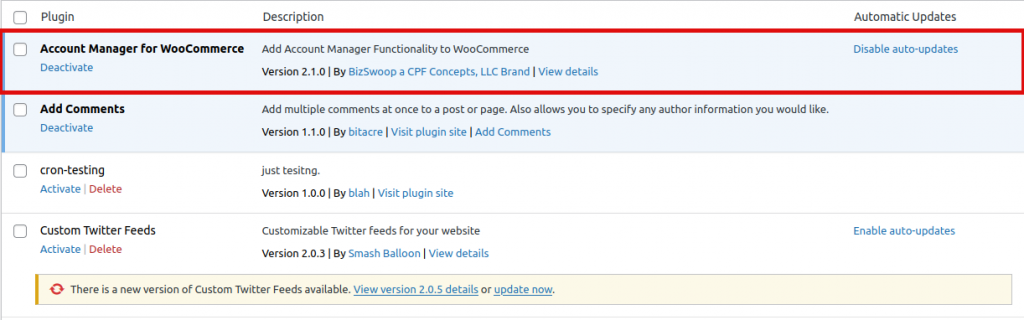
You can see the first plugin “Account Manager for Woocommerce” have auto-updates enabled. Because it says “Disable auto-updates” on the right, which makes sense because clicking that link will disable the enabled auto-updates. And it is up to date.
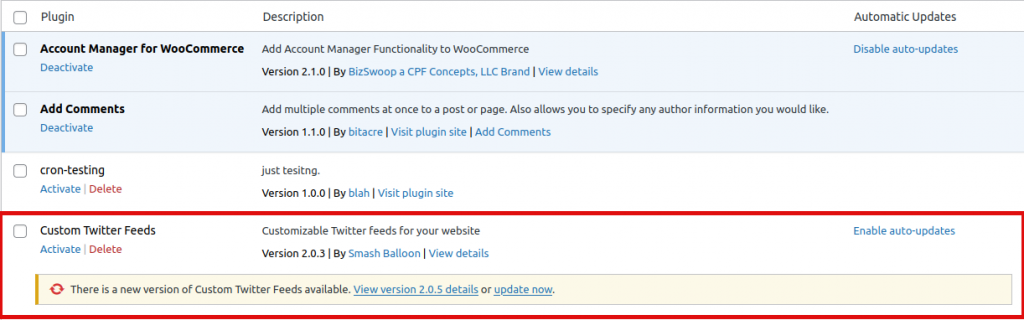
The last plugin, “Custom Twitter Feeds” has auto-updates disabled. Because inversely the link says “Enable auto-updates”. WordPress also makes it very clear a new update is available and encourages me to update now. Which is great, it is good to communicate this to the users.
The two middle plugins, however, say nothing here. Why is that they lack any information?
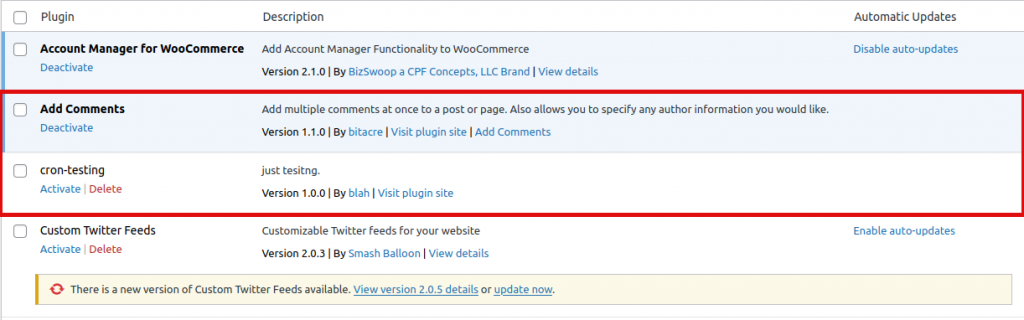
It appears if WordPress cannot find a source to update the plugin from, it simply stays silent about auto-updates.
The third example “Cron-testing” was a custom plugin I wrote to test some stuff related to Unpredictable WP-Cron problems. This makes sense that no update would be available because it is a one-off plugin.
The second plugin, however, is “Add Comments“. Notice it says nothing on the right. Yet, this plugin was originally downloaded from the official WordPress.org repository.
This lack of notification is the silent threat hiding in WordPress panels. This plugin was abandoned and un-updateable. It was disabled in the repository due to security issues. This is correct, the plugins team should disable plugins that have security issues. However, the important information, that has security issues, does not make it into the end-users dashboard.
It may be hard for the WordPress application to differentiate one-off plugins from abandoned plugins. So, for now, it may be up to you to make sure you look for un-updateable plugins in your dashboard. Or consider using a service like the Patchstack App that will notify you when you are running known insecure components.
Vulnerability roundup
This week’s vulnerability roundup highlights three plugins with no patches available for security bugs. Each has an unpatched security bug which could make sites vulnerable to exploitation. Users are encouraged to disable the plugins and find alternatives as soon as possible.
- be-popia-compliant – Unauthenticated SQL injection
- tags-cloud-manager – Unauthenticated XSS
- admin-side-data-storage-for-contact-form-7 – Unauthenticated XSS
Thanks and appreciation
This week’s thanks go out to all of the plugin developers that are actively maintaining your projects. Remember listeners, most security bugs do get patched, Just not all.
A special thank you goes out to the team over at Kadence for putting on Kadence Amplify this week. If you missed this event, you can check out the replays for all of the talks. I encourage you to do this, there were some insightful thoughts shared.
And thank you for your time listening to my security tips, tricks, opinions, and news on the Patchstack Weekly Security Update!


